Create a Digital Signature
In today’s digital world, paperwork is rapidly becoming a thing of the past. Whether you’re signing a contract, approving a payment, or filing taxes, everything is going electronic—and digital signatures are at the core of this revolution.
But what exactly does it mean to create a digital signature, and how can you ensure your signatures are secure, legally valid, and easy to use?
This comprehensive guide walks you through everything you need to know about digital signatures—what they are, how they work, where they’re used, and step-by-step instructions to create one. Whether you’re a business owner, freelancer, or government official, this article is tailored to help you make the switch to secure digital signing in 2025.
Why Should You Create a Digital Signature?
Here’s why individuals and businesses worldwide are switching to digital signatures:
Legally binding in many countries (e.g., eIDAS in the EU, IT Act in India, ESIGN Act in the US)
- Eliminates printing, scanning, and mailing delays
- Improves document security
- Reduces paper waste and operational costs
- Enables remote business operations from anywhere
Whether you’re closing sales deals, signing NDAs, or onboarding clients, creating a digital signature simplifies your workflow and enhances professionalism.
How to Create a Digital Signature?
Creating a digital signature is easier than you think.
Here’s how to do it using common tools:
Option 1: Use Online Signature Generators (Best for Beginners)
Platforms like DocuSign, Adobe Sign, Smallpdf, and HelloSign allow you to sign documents online securely.
Steps:
- Go to a trusted digital signature platform like Smallpdf eSign or DocuSign.
- Upload the document (PDF, Word, etc.).
- Click on “Add Signature.”
You can:
- Draw your signature using a mouse or touchpad
- Type your name and choose a font
- Upload a scanned image of your signature
- Drag and drop your signature into the document.
- Click “Finish” or “Save” to download your digitally signed file.
Tip: Always verify if the tool is compliant with regulations like eIDAS, ESIGN, or IT Act, depending on your location.
Also Read: How to create and add digital signatures to your email?
Option 2: Create a Digital Signature Using Software (Advanced Users)
If you require higher levels of cryptographic security—say for financial, legal, or government use—you can create a digital signature using certificate-based software.
Example: Using Adobe Acrobat (With Digital ID)
- Open Adobe Acrobat.
- Go to Tools > Certificates.
- Choose Digitally Sign.
- Use your Digital ID to sign. You can get this from authorized Certificate Authorities (CA) like eMudhra, GlobalSign, or DigiCert.
- Adobe will prompt you to draw/select your signature and validate using your credentials.
- The document is encrypted with your digital certificate and ready to send.
Read More: Kinds of Digital Signature
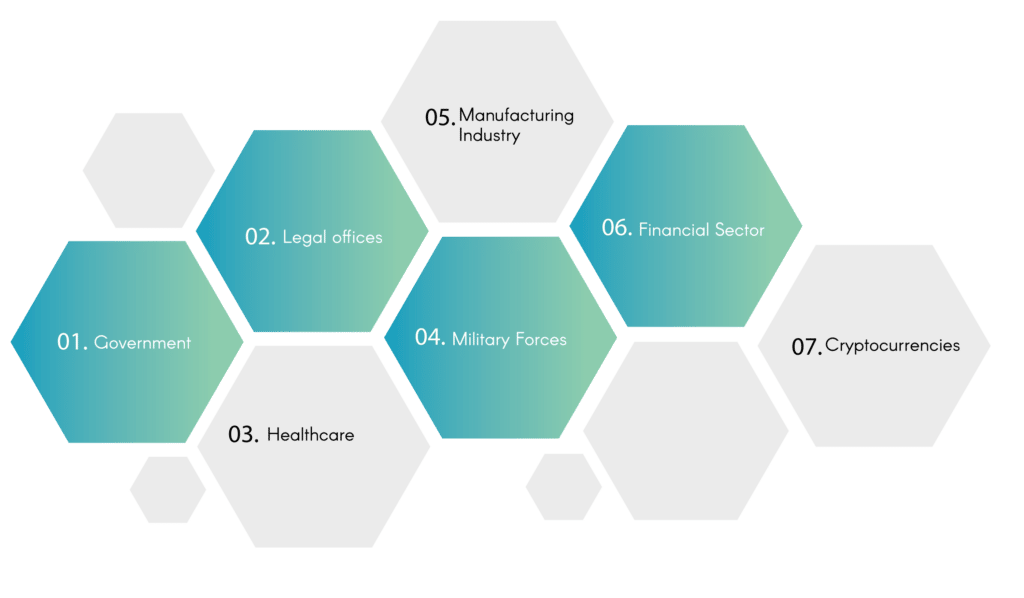
Where are Digital Signatures Used?
Every day, the impact of digital signatures is becoming more obvious. Many companies have begun using it to increase efficiency while ensuring the integrity of crucial documents. Let’s look at some of the important digital signatures expected to be utilized in 2022.
- Government: Due to its cost-effectiveness and high security, government agencies have begun to utilize digital signs. The government is involved in almost everything, from introducing new laws, tax returns, contract administration, identification cards, and many more. These are all essential documents requiring a digital signature to remove the requirement for a third party to be involved. This makes the process easier and minimizes the possibility of leakage.
- Legal offices: Legal offices are responsible for some of the nation’s most sensitive documents. Digital signatures have drastically reduced the expense of paper and labour. Security of documents is also an issue.
- Healthcare: Creating a digital signature has significantly improved the administration process for health care and treatment.The admissions process is now quicker, and data security has been enhanced.
- Military Forces: The military is among the most crucial and sensitive areas of any nation and has significantly benefitted from the advent of the digital signature. Particularly, security and information compartmentalization has increased 10-fold.
- Manufacturing Industry: To improve the efficiency of the process, manufacturing companies uses digital indicators. This improves the design of products and the quantity of products and sales.
- Financial Sector: The modern-day banking system has reached its peak through paper-free banking, contracts and loans that are quick. Creating a digital signature has made this possible.
- Cryptocurrencies: Cryptocurrencies can be a bit complicated, and blockchain authentication is performed by using create a digital signature. Digital signatures can also be utilized to verify bitcoin transaction details and help determine the ownership.
Looking to start an information technology business abroad? Speak with our business formation experts today.
What is PKI?
The Public Key Infrastructure (PKI) is a set of software as well as hardware and processes for managing digital signatures safely. Two keys are utilized in every digital signature process: A public and private key. Everyone who has to confirm the create a digital signature of the signer will be able to access this public key. The private key of the signer isn’t divulged to anyone else and is only used to sign documents electronically.
PKI also requires the use of an authority for certificates (CA) as well as enrollment software and a digital certificate, indispensable management tools, and certificate management.
Conclusion
The public key that is used to sign and create a digital signature is included in a digital certification that identifies the person who is associated with the key. Trusted authorities usually issue digital certificates that are valid for a specified period of time.
The certificate authority serves as the certificate’s security. This blog can help you create digital certificates that include digital signatures online.
FAQ’s
What is the time it will take to make an electronic signature?
DSC issuance would require 5 business days from the date of applying/application.
Can an individual be a digital signature?
A person may have multiple DSCs, but the majority of government websites are required to meet the need to register the DSC on the government server. Once registered, no additional DSC can be used until an additional DSC has been registered.
What is the length of time an electronic signature good for?
Electronic signatures are valid for a period of time and have an expiration time of 0 days. Documents that have been signed using electronic signatures using Adobe Sign are certified document that has been sealed with Adobe’s certification.
What happens if a digital signature gets lost?
In the event that you lose your certificate or it gets stolen, the E-Token or I-Key was stolen the person must cancel his certificate and apply for another one. The certificates issued will be valid for 1 year or 2 years, and must be renewed.

